SCHEDULE
Monday, July 18, 2022
08:50 – 09:00 Welcome and Opening
09:00 – 11:00 Prof. Leo Storme
11:00 – 13:00 Dr. Ilaria Chillotti
13:00 – 14:00 Break
14:00 – 14:20 Gianira Alfarano
14:30 – 14:50 Chistopher Battarbee
15:00 – 15:20 Elena Berardini
15:30 – 16:00 Break
16:00 – 16:20 William Cocke
16:30 – 16:50 Marialaura Noce
17:00 – 17:20 Wyra K. Kadir
Tuesday, July 19, 2022
09:00 – 11:00 Dr. Ilaria Chillotti
11:00 – 13:00 Prof. Alberto Ravagnani
13:00 – 14:00 Break
14:00 – 16:00 Prof. Kahrobaei Delaram
Wednesday, July 20, 2022
09:00 – 11:00 Prof. Alberto Ravagnani
11:00 – 13:00 Prof. Leo Storme
13:00 – 14:00 Break
14:00 – 16:00 Prof. Kahrobaei Delaram
Thursday, July 21, 2022
09:00 – 11:00 Programming Session
11:00 – 11:20 Anina Gruica
11:30 – 11:50 Vincenzo Pallozzi Lavorante
12:00 – 12:20 Monika Trimoska
12:30 – 12:50 Valentino Smaldore
13:00 – 14:30 Break
14:30 – 18:00 Programming Session
Friday, July 22, 2022
09:00 - 09:15 Prof. Massimiliano Sala
09:15 - 10:30 Bluenet
10:30 - 11:00 Break
11:00 - 11:40 Umberto Sorbo
11:40 - 12:20 Antonella Cioffi
12:20 - 13:00 Alfonso Tramontano
13:00 - 13:15 Best Presentation Award and Closing Session
Lectures (16 hours)
Introduction to FHE and the TFHE scheme (Dr. Ilaria Chillotti, Zama - France)
Fully Homomorphic Encryption (FHE) is a new technology allowing to perform computations over encrypted data.
Since the first solution was proposed in 2009, the research has done huge steps forward: operations that were realizable in the order of hours or even days of computation, nowadays can be performed in a matter of milliseconds.
FHE is mainly interesting at this moment because it represents a powerful solution to solve many problems related to the privacy of sensitive data: medical, financial, genomic, and so on.
This data already circulates on the internet, but is only encrypted in transition or when it is stored on a server. However, in order to be manipulated, it needs to be decrypted. With FHE, data could remain encrypted end-to-end, so privacy would be protected and the functionalities offered by service providers still ensured.
Many FHE schemes have been proposed in the literature and are implemented. In particular the ones that are mainly studied and used at the moment are the ones based on the hard lattice problem LWE, which is one of the most promising solutions for the post-quantum era.
These classes are going to be split in 2 major parts:
- In the first part we will introduce FHE in general and we will do an overview of existing schemes and their implementations.
- In the second part, we will focus on one of these schemes, TFHE, and we will show some applications and experimental results.
Group-based cryptography in the quantum era (Prof. Delaram Kahrobaei, City University of New York - USA)
In these two lectures we present an overview of the current state-of-the-art in post-quantum group-based cryptography. We describe several families of groups that have been proposed as platforms, with special emphasis in polycyclic groups and graph groups, dealing in particular with their algorithmic properties and cryptographic applications. We then describe some applications of combinatorial algebra in fully homomorphic encryption. In the end we discussed several open problems in this direction.
Network coding (Prof. Alberto Ravagnani, Eindhoven University of Technology - Netherlands)
The course offers an introduction to the idea behind network coding, namely allowing the intermediate nodes of a communication network to combine information packets before forwarding them. In the second part of the course I will focus on error correction in the context of network coding via rank-metric codes.
Linear Codes and Galois Geometries (Prof. Leo Storme, Ghent University - Belgium)
Many problems in coding theory are equivalent to problems in finite geometry [1]. Often these links arise via the columns of a generator matrix or the columns of a parity check matrix for a linear code.
Classical examples include:
- Linear codes meeting the Singleton bound and arcs in finite projective spaces,
- Linear codes meeting the Griesmer bound and minihypers in finite pro- jective spaces,
- Covering radius of linear codes and saturating sets in finite projective spaces,
- Small weight codewords in the linear codes arising from the incidence matrices of finite projective spaces,
- Strong representative sets/Tangency sets in finite projective spaces and the rank of incidence matrices of finite projective spaces.
Finite geometry has succeeded in solving many equivalent geometrical prob- lems from coding theory, but, also vice versa, coding-theoretical techniques have contributed to the solution of geometrical problems.
More and more links are kept being found.
This course will discuss a number of the links between coding theory and finite geometry.
[1] L. Storme, Coding Theory and Galois Geometries. Chapter 14 in Concise Encyclopedia of Coding Theory. (W.C. Huffman, J.-L. Kim and P. Solé, Eds.) Chapman and Hall/CRC Press, Discrete Mathematics and Its Appli- cations (2021), 285-305.
Programming Session (5 hours)
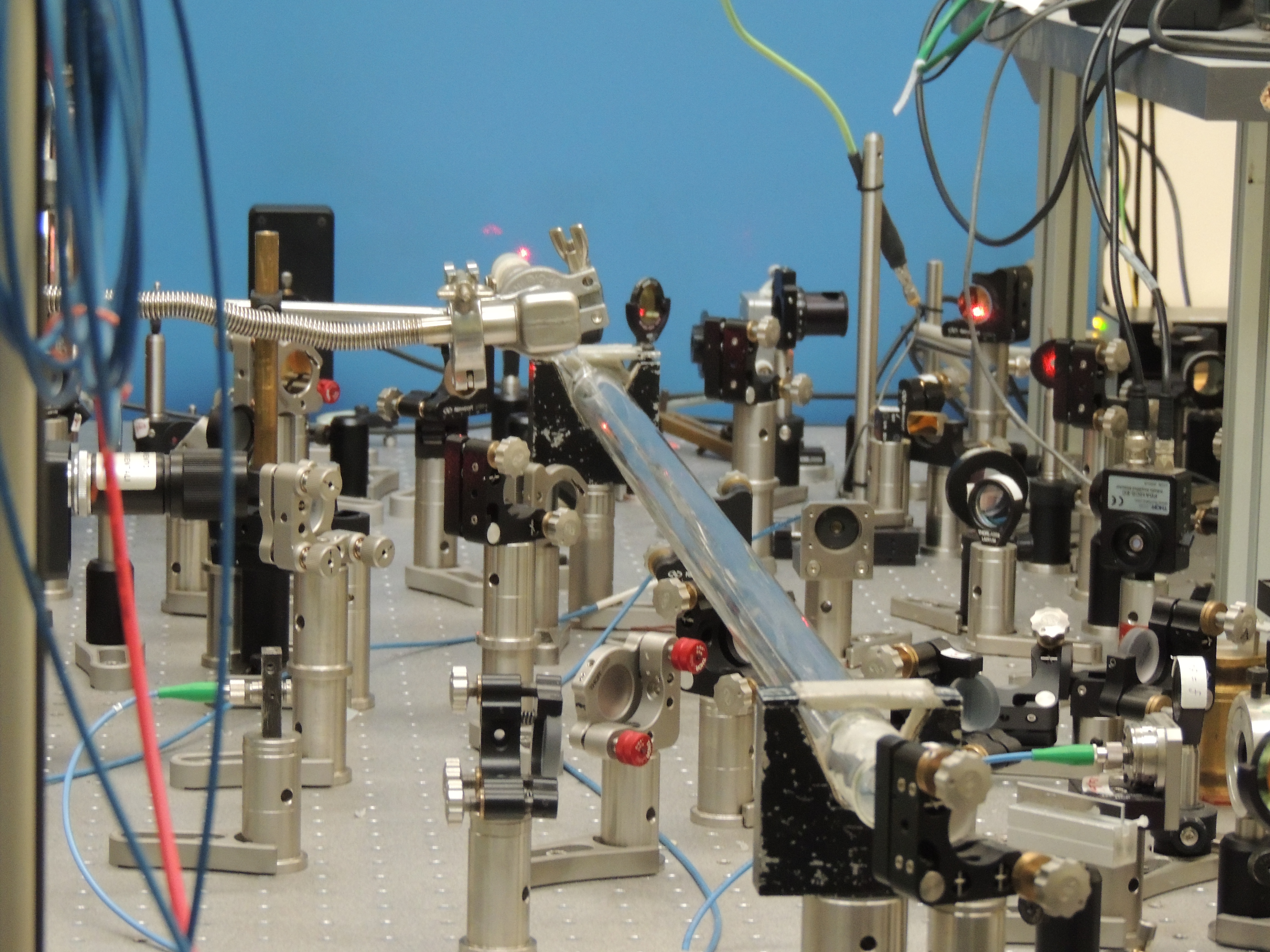
Experiencing formal modelling and analysis of protocol security with the Tamarin Prover (Dr. Mariapia Raimondo, Università degli Studi della Campania Luigi Vanvitelli)
As computer-based communication and processing is getting more and more important in modern societies and economies, the necessity of ensuring some critical features of such communications is of paramount importance. Proper cryptographic schemas are the card to play to guarantee the security of these protocols, since choosing the wrong way to share information over insecure channels may compromise the security of the whole system. Such critical services and systems need sophisticated verification and validation procedures that rely on methods for modelling and formal analysis.
Hence, in the last decades there has been a lot of focus on automatizing the verification of security protocols, since it might be a very long and meticulous task, in particular for very large protocols. For this reason, a great effort has been made by the research community to specialize "general purpose" formal methods to take advantage of specific features of such protocols and, thus, to improve tool scalability.
One of these tools is the Tamarin Prover, which is a symbolic model checker revealing its full potential in the modelling and analysis of security protocols.
The course is divided into two lessons. After giving a gentle introduction to model-checking and security properties, the first part will provide the basic concepts of the syntax and semantics of the Tamarin Prover with the discussion of some examples (2 hours). The second part of this tutorial will see participants experimenting and getting familiar with the tool by writing a simple protocol and checking its properties (3 hours).
Business Session (4 hours)
Digital Stamp (Ing. Nicola Fedele - CEO, Ing. Dayton Martucci, Bluenet srl)
Being secure of the identity of people is a paramount importance in these days: public order forces as well as private guards are often unable to verify electronic devices due to the short time to check the identity. The speech will introduce a mechanism based on the recognition of image and text where the identity information and secure codes are embedded into high density QR code on a plastic card. By means of simple mobile apps, a policeman can verify in real-time the consistency of the QR code with the plain image and text.
Secure element technology and Cryptography (STMicroelectronics)
The speech will introduce secure element and smart card technology and their role in securing applications, protocols and user data. It will contain examples of advanced applications in various domains (like telecom, banking, IoT…) that use secure element and their link with cryptography. It will provide an overview of sophisticated hacker attacks (like fault injection, power analysis…) and of the hardware/software countermeasures that are typically in place. Finally, it will introduce the role of the secure element in Fully Homomorphic Encryption.
Community Session
De Componendis Cifris, the Italian crypto community (Prof. Massimiliano Sala, Università degli Studi di Trento, Acting Director of Decomponendis Cifris)
In October 2017, under the guidance of the late Michele Elia, forty people met in Rome with the aim of creating an Italian initiative that gathers all cryptographers willing to cooperate for the good of our nation. Now, more than one thousand people are regularly involved in our many activities: from a dozen mailing lists and seminar series, to the publication of two book series, to the planning and organization of complex projects involving universities and companies. A special emphasis is given to the opening of the academic world towards an outside modern environment, where cryptography is more and more in demand. Dozens of internships and stages for students, the reorganization of entire degrees, the federation of several universities in the so-called Advisory Board, these are all witnesses to the success of De Componendis Cifris.
Contributed Talks